53 Discuss various unsecure methods for accessing devices across the network Telnet
It is a terminal emulation protocol that provides the functionality of remote login access to devices over the network. The Telnet connects the host to the devices through the network with the help of TCP/IP. Telnet transfers the text from the host to the destination in form of clear text.
HTTP
It is another unsecure method that manages the communication between the web browser and the server. HTTP runs by default on TCP port 80. HTTP defines the action the web server and browsers should take in response to the various commands. HTTP has the major disadvantages that it does not remember the commands that the user previously executed. It also does not remember user's preference on websites they visit. To provide this functionality HTTP has to use other technologies such as Javascript, AJAX and other server side scripting languages.
FTP
File transfer protocol is used to transfer files. FTP uses TCP port 21 and 20 by default. It is used to transfer data in large quantity from web servers. FTP has advantage over HTTP in case of speed. FTP transfers the data from the client to the server in secure manner. User must have an username and password to access FTP sites and transfer data.
FTP uses to components:
1) FTP Server
2) FTP Client
FTP Server: They are the servers which presents the data to be transferred. FTP servers can be configured very easily. We can set up our system as a FTP server. Microsoft Windows have build in FTP server capability as it is with Linux. FTP servers major disadvantages is that they are not secure they should not be used in case of transferring important data over the internet.
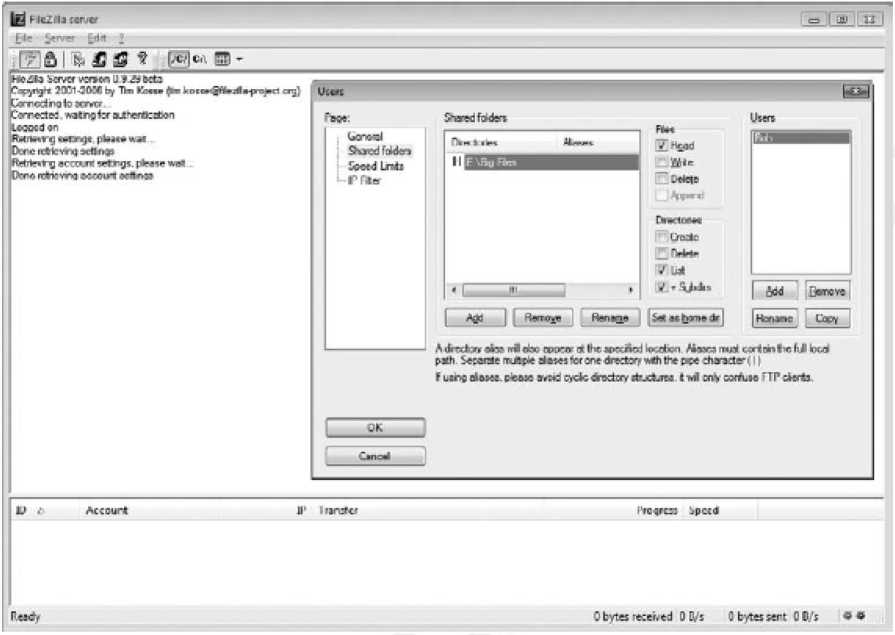
Figure 87: An example of FTP server
FTP client: Anyone with a FTP username and password can connect to the FTP server via web browser. To connect to FTP server we need the following things:
1) Address of the FTP website
2) Username
3) Password
Examples of FTP clients are Mozilla Firefox, Internet Explorer and Opera etc. but these clients offer limited functionality. In order to use complete functionality of FTP use FTP clients. Example of FTP clients are FireFTP, FileZilla etc.
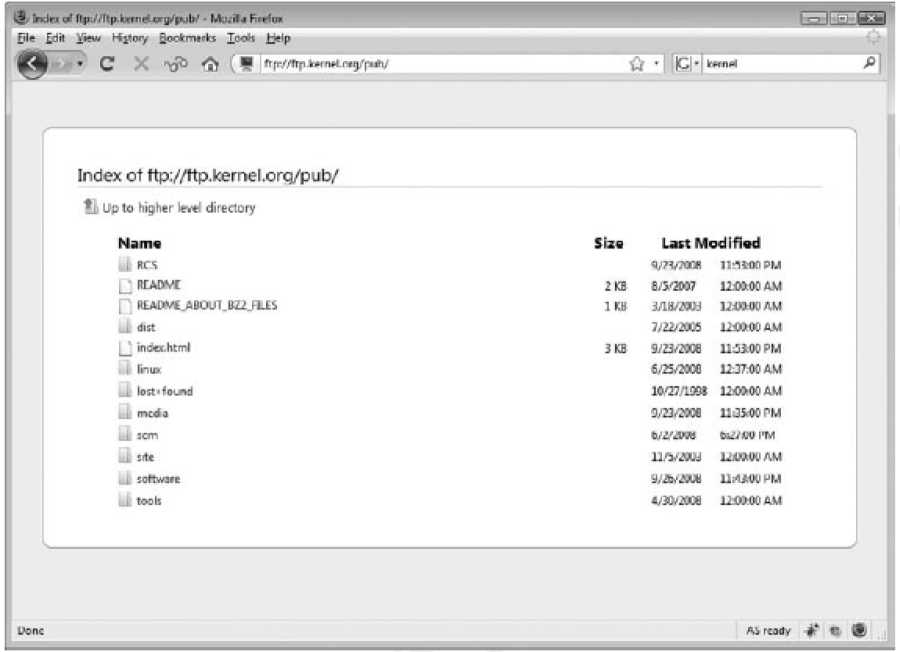
Figure 88: Web browser running FTP
Remote Shell (RSH)
It allows us to send single commands to the remote server. It runs over the TCP port number 514. RSH was originally part of the UNIX operating system. The main disadvantage of the RSH protocol is that it is not secure. RSH sends unencrypted information over the network. This information can be used by the network attackers to gain sensitive information about the network.
Remote Copy (RCP)
It is an utility to copy files from the web server without the need of FTP and NFS (Network File System). RCP uses the TCP port number 514 and can used in scripts.
SNMP v1/2
Simple Network Management Protocol (SNMP) is the network management protocol which queries the SNMP capable devices. It uses the concept of SNMP agent and SNMP server. The SNMP versions 1 and 2 are not secure as compare to SNMP version 3. SNMP version 3 added more security functionality to the SNMP. There are various SNMP tools available in the market such as from Cisco or Cacti.
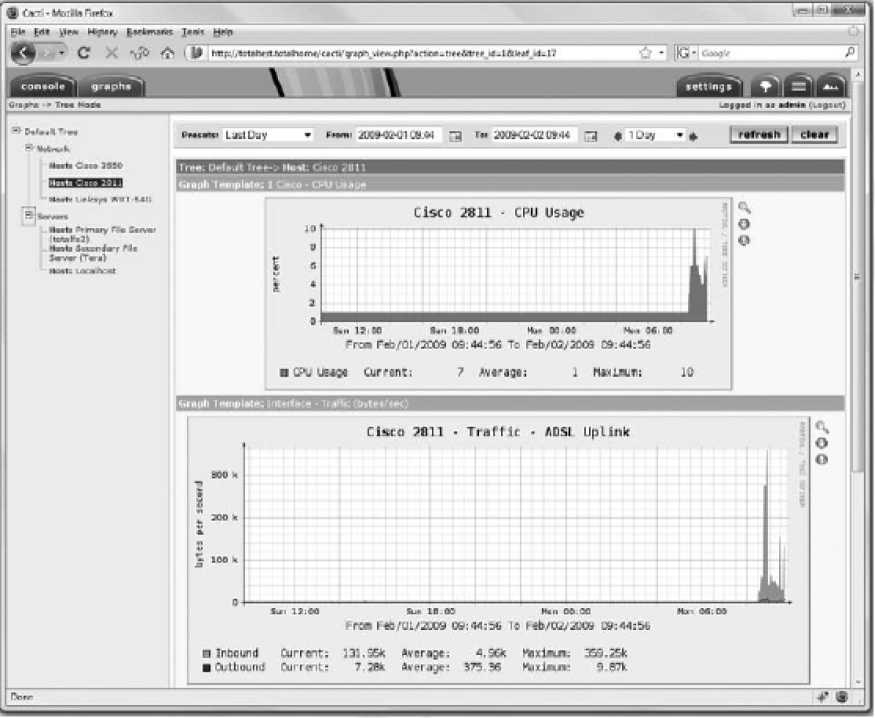
Figure 89: SNMP configuration on Cisco routers
access-list 10 permit 10.0.0.0 0.0.0.255
snmp-server community public RW 33
snmp-server location B1
snmp-server contact helpdesk@network.in
snmp-server chassis-id 2511_AccessServer_Canadice
snmp-server enable traps snmp
snmp-server enable traps hsrp
snmp-server enable traps config
snmp-server enable traps entity
snmp-server enable traps bgp
snmp-server enable traps rsvp
snmp-server enable traps frame-relay
snmp-server enable traps rtr
snmp-server host 10.0.0.2 public
