41 Describe various methods used for network protection
The various methods used for network protection are:
- Intrusion Detection Software
- Intrusion Prevention Software
Intrusion Detection: It is an application that can run on computer or a dedicated machine. Its task is to monitor the incoming packets and look for intrusion into the system. On seeing the attack the IDS have the capability to inform the network administrator via email, pop up message or even a text message to phone.
There are two types of IDS
1) Network based IDS (NIDS)
2) Host based IDS (HIDS)
Network based IDS: It has multiple sensors placed on inside and outside of the network gateway. The sensors read the packets and reports to the centralized application which in turn read the signature file for detect suspicious activity.
Host based IDS: It is an application running on the system that monitors the system from system file changes or registry changes.
An organization that cares for its security has both NIDS and HIDS where NIDS works on the incoming/outgoing traffic and HIDS works on the individual computers.
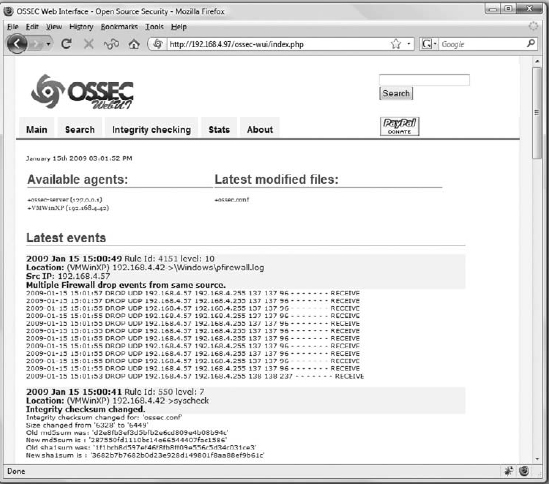
Figure 69: HIDS
Intrusion Prevention: This is a process used to safeguard our network from the outside/inside attacks. This software has the capability to react when there is a network attack. An Intrusion prevention system blocks the packets based on ip address, ports, or application.
