Section 5.2: Encryption Technologies
Encryption refers to the cryptographic algorithms that are used to encode plain text into non-readable form or cyphertext to ensure security or the privacy of the text. The receiver on the other side uses a decryption key to bring the message it to its original plain text form.
There are three main encryption algorithms, as shown in Figure 68:
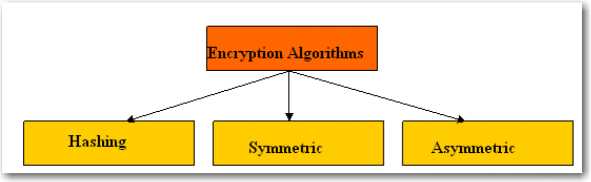
Figure 68
Section 5.2.1: Hashing algorithm
Hashing algorithm takes data message and converts the message to a numeric value, which is called the hash total or value. Hashing can be one-way or two-way. A one-way hash doesn't allow message to be decoded but the two-way hash allows the message to be reconstructed from a hash.
When a one-way hashing algorithm is used to generate the message digest the input cannot be determined from the output. Hashing is most commonly used to encrypt and decrypt digital signatures and passwords. There is no way to determine the original text based on a hash. You only need to verify that the hash for the password you are giving. The system now matches the hash in your user profile. Hashing is mainly used to verify the integrity of a given bit of data. Even if one bit had changed the resulting hash would be different and you will know that some tempering has been done with the data.
The two main hashing standards for encryption that exists are:
- SHA (Secure Hash Algorithm): SHA was designed by the National Security Agency (NSA) and published by the NIST. It is a one way hash that provides a hash value that can be used with the encryption protocol. It produces a 160-bit hash value. The three SHA algorithms are structured differently when SHA was updated and was distinguished as SHA-0, SHA-1, and SHA-2.
- MDA (Message Digest Algorithm): MDA is also a one-way hash and takes a message of arbitrary length as input and produces a 128-bit "fingerprint" or "message digest" of the input. There are several versions of MDA. Most common versions are MD5, MD4, and MD2
Section 5.2.2: Symmetric Algorithm
Symmetric-key algorithms require cryptographic keys for both decryption and encryption. The key are usually same and is shared between the two parties. The keys in symmetric-key algorithms is said to use a shared secret between two or more parties to maintain a private information link. The shared key is considered a disadvantage of this algorithm. The secret key is sometimes called the private key. If the key is lost then the entire process is breached. They are however, much faster as compared to asymmetric key algorithms.
Section 5.2.3: Asymmetric algorithm
Asymmetric key algorithms use different keys for both encryption and for decryption.
The keys are referred to as public key and private key. The public key is used to encrypt the message and the private key is used to decrypt the message by the receiver. The public key is truly public and can be shared between two or more parties but the private is only known to the receiver.
Section 5.2.4: Data Wiping
Usually the hard drives that are no longer in use are recycled and sold. However, sometime the hard drives that you want to discard store important and confidential information of your company that should not fall into the wrong hands. Usually when you format a hard drive then the information on the drive is not wiped out. You may think it's gone, but it really isn't.
All that really happens is that the space on your hard drive where the file(s) used to reside is flagged as over-writable. The only way to ensure that your files are completely gone is to wipe your drive clean. Data wiping is done only if your drive contains sensitive information. It totally obliterates a file so it can not be recovered.
Section 5.2.5: Software Firewall
The software firewall is application software that filters the network traffic to and from a computer. It inspects network traffic passing through it and permits or denies communications based on a security policies configured in the firewall. It acts like a gate between a protected network and an unprotected network that ensures that nothing private goes out and nothing malicious comes in. However, without proper configuration, a firewall can become worthless. The configuration requires detailed understanding of the network applications and the endpoints for the organization's day-to-day operation.
Firewall functions as one or more of the following:
- Packet Filter: A packet filtering firewall examines each packet crossing the device for five characteristics: Source IP address, Source port, Destination IP address, Destination port, and IP protocol. For example it can block web traffic on port 80 and telnet traffic on port 23. It also inspects the packet headers of all network packets going through the firewall. Based on the firewall rules, the firewall either allows, drops, or rejects a packet. If a packet is rejected, the firewall sends a rejection message back to the sender. If the packet is dropped, the firewall does not respond to the packet and the sender has to keep waiting for the communication to time out. The exceptions to the rules can be configured in packet filtering to exceptionally allow a particular type of packet. Packet filtering firewall operates on Layer 3 Network Layer of the OSI model.
- Proxy Firewall: The application-proxy firewall examines every packet that crosses the firewall and compares against the firewall rules. If the packet passes the examinations, it is re-created and is allowed to pass through the firewall. This type of firewall destroys and re-creates each packet and can therefore prevent unknown attacks based upon TCP/IP weaknesses. It also hides the internal network addresses from the outside world.
- Stateful Inspection or Stateful Packet Filtering: The stateful packet filtering keeps a track of the state of network connections, such as TCP streams and UDP communications that passes through it. It can find out the legitimate packets for different types of connections and allows only those packets that match a known connection state.
